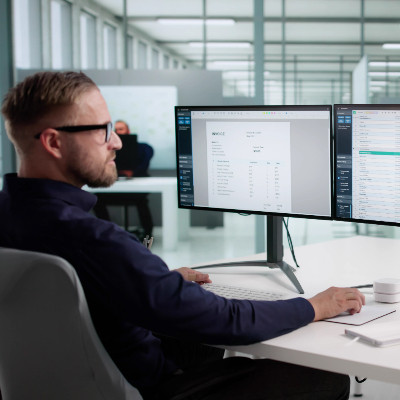
When you think of business technology, what’s the impression you get? Do you look at it as a pain in the neck obligation, an unavoidable cost, or one of your most valuable assets?
For many, it is the former… but for the most successful among us, it is the latter. Let’s talk about how you can use your technology to optimize your incoming cash flow.