The way businesses use technology has completely changed over the last ten or fifteen years. Organizations have transitioned from localized physical machines to running entire operations on a distributed digital network. Yet, a lot of business owners are still stuck with an IT framework left over from 2010.
Datalyst Blog
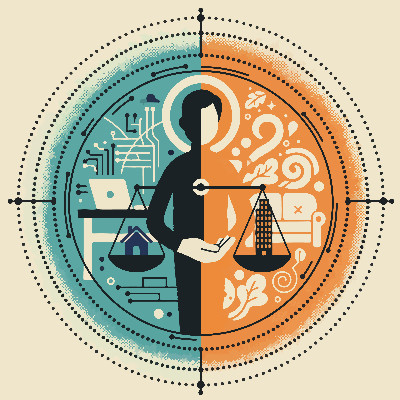
Most business owners assume that tighter security requires a slower user experience. They accept friction as the price of safety.
This mindset creates a dangerous paradox: when security is too difficult to use, your team becomes less secure. If logging in requires three different devices and ten minutes, employees will work around you. To eliminate this invisible productivity and security leak, you must remove friction.
How much of every week do you, or any of your employees, spend seeking out the information needed to get the job done… or trying to, at least, in between all the diversions and distractions. How often have you trawled through your digital storage, only to lose track of your progress when yet another chat notification drags your attention away from… what were you working on again?
How frustrating is it when your computer just doesn’t want to cooperate, whether it takes its sweet time starting up in the morning or decides to go on break in the middle of a meeting? How frustrating it is to see it happening to your team members, fully aware that they are feeling the same frustration you would? How much does it cost you, all events converging over time?
How much of a relief would it be if all these problems stemmed from one source: it being the time to retire that particular piece of hardware and replace it with something new?
For many, the introduction of remote or hybrid work practices was less of a choice and more of an existential need. Now, years after certain events caused this existential need, there are still pockets of friction that appear and make these approaches to work far more challenging than they can and should be.
Let’s explore a few of these pockets of friction and even more crucially, how to smooth them over.