Datalyst Blog
UTM: The Ultimate Defense for Businesses
While most businesses take data security seriously these days, there is still a tendency to treat each area of concern with different solutions. One application to filter content, one for spam protection, another for viruses, and still another solution for firewall protection. Instead of trying to force different pieces of software and hardware to speak to each other, invest in an all-in-one solution: a UTM.
What is a UTM?
A UTM (Unified Threat Management) solution combines a variety of standard security measures into one easy to manage device. With a UTM place, your business manages one device, as opposed to several pieces of software and hardware. This reduces the possibility of security ‘holes’ due to misconfigured or incompatible software. As a UTM is hardware-based and self-contained, it's the ultimate turnkey security system for your business.
Benefits of a UTM
A Unified Threat Management device benefits your business by combining a firewall with network security, providing comprehensive security. Here are some ways a UTM can benefit your business.
Increases Productivity With Content Filtering
A UTM can increase productivity by restricting the type of content your team is allowed to access during work hours. Unfortunately, your team can find themselves distracted and focused on other issues (besides their workload) when they can access some types of content. Some of this content can include:
- Job searches
- Streaming services like Netflix, Hulu, and Twitch
- Social networking websites
- Adult-oriented websites and file sharing sites
When you utilize content filtering, not only do you increase productivity, you also reduce the opportunity for team members to access malicious websites, exposing your business to malware and other types of viruses, most notably ransomware.
Firewall and Virus Protection
A firewall (software or hardware) is one of the most important security measures your business can invest in. A firewall keeps intrusions out of your network and your data secure. However, a firewall is only as effective at keeping your business safe as the team that it protects is at following best practices.
Unfortunately, one of the biggest risks for network compromise will come from your team members themselves. Team members can fall for phishing attacks and otherwise expose the network to attack. This is why firewall security--when combined with the spam and virus protection that a UTM provides--is invaluable to keeping your network secure.
How A UTM Works
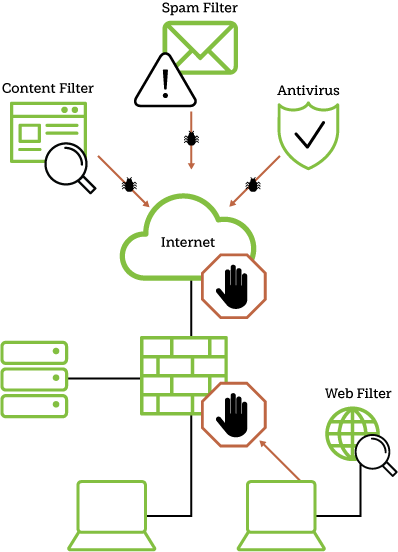
Unlike solely software solutions which protect your network after it has potentially been breached, a UTM works as a physical ‘barrier’ between your network and the internet. One way to think of a UTM is as a firewall + virus protection + content filtering + email security all in one device.
Since a UTM is a single device, it allows your business to control and maintain your business’ network security from a central location. This removes the necessity to update the security of all of your workstations individually, allowing for consistent levels of protection, particularly in a multi-generational OS and workstation office.
Are You Ready To Protect Your Business?
A piecemeal network security plan can’t provide the level of security that a UTM can. By eliminating compatibility issues with an all-in-one UTM Solution, Datalyst can ensure your business and your data reaches a new level of security. It only takes one hole in your security for your entire network to become compromised, but a UTM device is the best way to keep those holes to a minimum. Interested in UTM, Managed IT or IT Services? Call (774) 213-9701 today to learn more.

